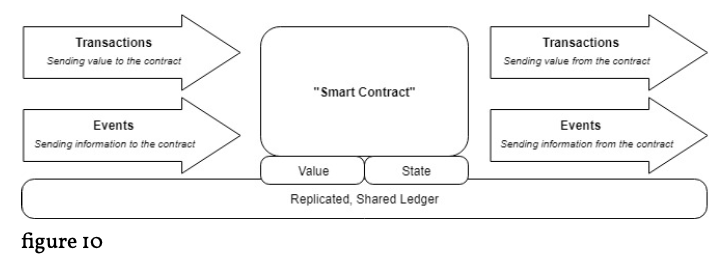
. . .to get a better understanding of possible attacking points and weak spots of the network we take a look on the actual chain structure. The structure enables three different identification possibilities for individual blocks. The first possibility of identification is through the individual hash (or identification number of the block) of each block. “One of the most popular hashing functions used in cryptography today is called Secure Hash Algorithm 256, or SHA-256 […]. Developed by the National Security Agency, SHA-256 is the hashing function that powers Bitcoin” (Guzzetta, 2018). This hash, however, is depending on the content of the block header and will change when some of the content in the block header changes. We remember that the “previous block header hash” (sometimes also called “reference”) points to and is identical with the overall hash of the previous block, and that this overall hash is dependent on and changes with the own reference in its own block header.1 If the content of a block is being altered, for example by adding a new transaction, it is then inevitably that the overall hash of the block is changing as well, leading to a break in the chain structure.2 Such altered block interrupts the chain and makes all following blocks invalid, shortening the chain. To maintain the length of the chain while tampering with it, one would need to compute all hashes of all subsequent blocks which would require immense computing power and is therefore very unlikely to succeed. The second possibility to identify a block in the BC is the so called “block height”.3
1Hoser & Fulbright, 2016.
2Siba, Tarun, & Prakash, 2016.
3Bitcoin.org-Developer-Guide, 2018.